
Protect Software – Software protection – Prevent software piracy
Protect Software
Protect Software from Piracy — 4 Powerful Software Protection Methods
Secure and deliver your software in minutes. No programming skills required whatsoever. Our powerful technology can protect almost any software type, including .NET and WPF assemblies.
Discover the best anti piracy software protection service and solutions to prevent piracy, cracking, and unauthorized use. Learn how hardware dongles, licensing, and encryption protect software globally.
Protect Software from Piracy with Advanced Software Copy Protection Solutions
Software piracy is a global threat that causes billions in losses each year. Protecting your applications requires a multi-layered software protection strategy combining licensing systems, software encryption protection, and hardware enforcement.
Why Software Protection Is Critical
Without protection:
❌ Software can be copied and shared illegally
❌ License keys can be cracked
❌ Revenue loss increases
❌ Intellectual property is stolen
With strong protection:
✔ Control distribution
✔ Enforce licensing
✔ Prevent reverse engineering
✔ Secure proprietary algorithms
Best Methods to Prevent Software Piracy
1. Hardware-Based Protection (Dongles)
Physical license keys ensure software runs only when the device is connected.
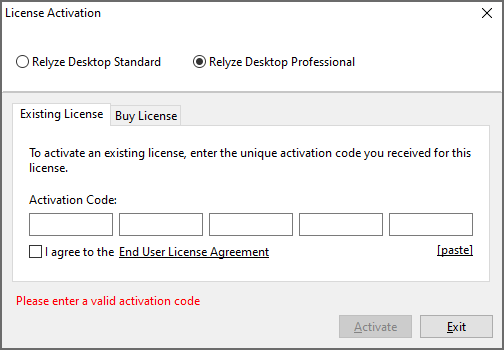
2. Software Licensing Systems
Activation keys and license servers control authorized installations.
3. Encryption & Code Obfuscation
Protect executable code from reverse engineering.
4. Online Activation & Verification
Prevents unauthorized duplication across devices.
5. Feature-Based Licensing
Sell different software tiers securely.
Advanced Software Copy Protection Technologies
- Anti-debugging protection
- Anti-tamper detection
- Virtual machine detection
- Secure key storage
- License expiration control
Enterprise solutions combine multiple layers for maximum security.
Supporting Articles
- Software Copy Protection Dongles Explained
- Best Anti-Piracy Tools for Developers
- How to License Software Securely
- Prevent Reverse Engineering Techniques
- DRM vs Hardware Licensing
🔐 Protect Software from Piracy — Complete Guide for Developers & ISVs


Software piracy costs the global software industry billions annually. Whether you sell desktop applications, engineering tools, enterprise systems, or proprietary utilities, protecting your software is essential to safeguard revenue and software intellectual property protection.
This guide explains how to protect software from piracy using proven technical, legal, and licensing strategies used by leading software vendors worldwide.
🛡️ Why Software Piracy Happens
Piracy occurs when users bypass licensing controls to use software without authorization.
Common Methods Used by Pirates
- Cracked executables
- Key generators (keygens)
- License sharing
- Reverse engineering
- Emulator tools for hardware keys
- Illegal redistribution
Without strong protection, even expensive software can be duplicated infinitely.
🚀 Most Effective Ways to Protect Software from Piracy
1. Hardware-Based Protection (Most Secure)
Using a USB hardware key (dongle) ensures the software runs only when the physical device is present.
Benefits
✔ Impossible to duplicate digitally
✔ Offline protection
✔ Strong encryption storage
✔ Prevents unauthorized copying
Ideal for high-value software like CAD, CAM, medical, industrial, and financial applications.
2. Software Licensing Systems
Implement license management to control installations and usage.
Licensing Models
- Node-locked license (single PC)
- Floating/network license
- Subscription licensing
- Trial licenses
- Feature-based licensing
License servers can monitor usage and enforce compliance.
3. Online Activation & Verification
Require internet activation to validate licenses.
Advantages
- Prevents mass distribution
- Detects suspicious usage
- Enables remote license revocation
Combine with device fingerprinting for stronger control.
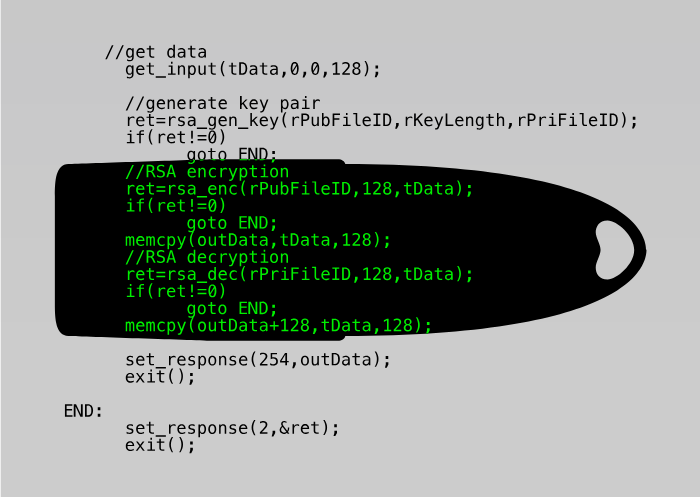
4. Code Obfuscation & Encryption
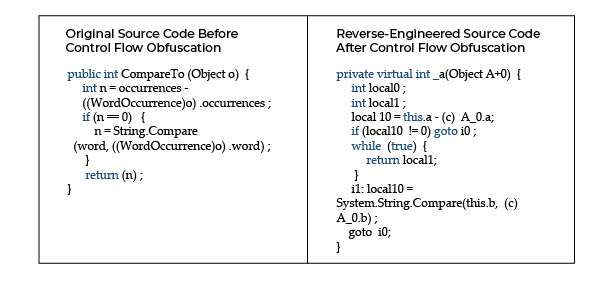
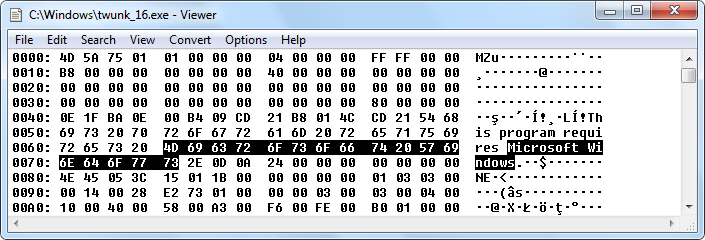

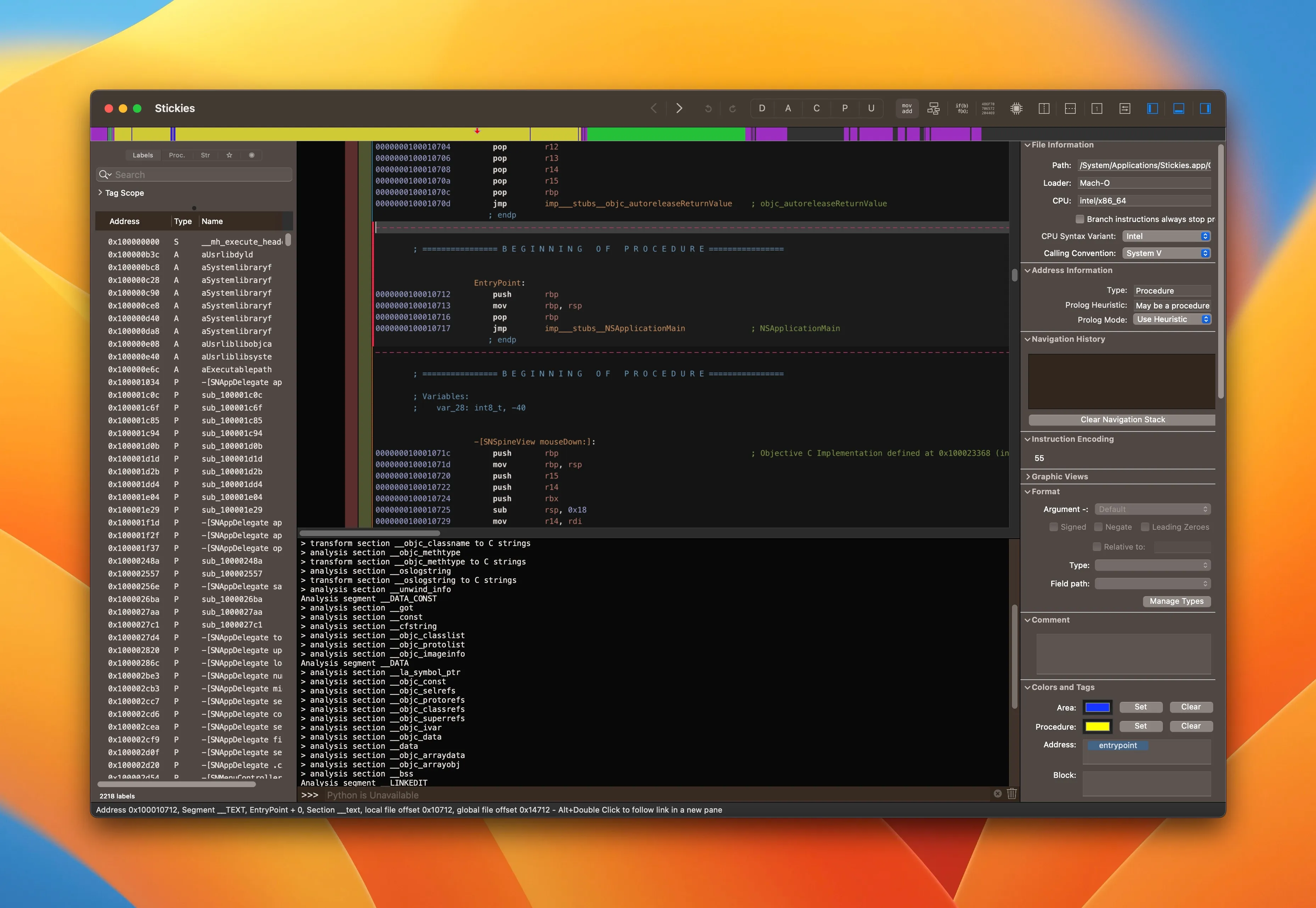
Protect your application binaries from reverse engineering.
Techniques
- Code obfuscation
- Binary packing
- Encryption of critical modules
- Anti-debugging protection
- Anti-tamper checks
This prevents attackers from understanding or modifying your code.
5. Digital Rights Management (DRM)
DRM controls how software is used, copied, and distributed.
DRM Capabilities
- Usage restrictions
- Device limits
- Region control
- License expiration
- Feature locking
Widely used in gaming, media, and enterprise software.
6. Secure License Storage
Store license data securely to prevent tampering.
Options include:
- Hardware dongles
- Secure elements
- Encrypted license files
- Trusted platform modules (TPM)
🌍 Advanced Enterprise Anti-Piracy Strategies
Multi-Layer Protection Approach
Top software companies combine:
- Hardware enforcement
- Software licensing
- Encryption
- Monitoring
- Legal protection
No single method is sufficient alone.
Monitoring & Analytics
Track suspicious usage patterns:
- Multiple activations
- Geographic anomalies
- Cracked version detection
- Unauthorized distribution channels
Legal & Compliance Measures
- License agreements (EULA)
- Copyright enforcement
- DMCA takedown requests
- Legal action against distributors
💼 Best Protection Strategy by Software Type
High-Value Commercial Software
➡️ Hardware dongle + licensing + obfuscation
SaaS Applications
➡️ Cloud licensing + authentication
Consumer Software
➡️ Activation + DRM
Offline Industrial Systems
➡️ Hardware-based licensing
🏁 Final Recommendation
The Strongest Protection Model
Hardware Dongle + Licensing System + Encryption + Monitoring
This layered approach delivers maximum security and global scalability.
Protect Software from Piracy
Protect Software from Piracy. Learn more about the software copy protection USB solutions from AFT INDIA offers to find the best fit supported technologies such as 4D, Access, AutoCAD, C and C++, Delphi, Excel, FileMaker, FORTRAN, Java, LabVIEW, MATLAB, .NET and ASP.NET, PDF Documents, PHP, Python, REALbasic/Xojo, WinDev for your use case. The Software Hardware Dongle is an electronic device designed to work with computer just like any peripheral devices. The Software Protection Dongle Keys are often referred as Hardware Lock, Hardware Key, Security Dongle, Security Key, Dongle Lock, Dongle Key and Port Lock.

Questions? Contact Sales – Software Copy Protection Dongle Price
Software application protection dongles provide highest security USB dongle for software licensing with hardware key security token features driverless dongle of software piracy protection key. Cross-platform dongle (Windows, macOS, Linux). Experience encryption dongle for software with our powerful anti-piracy hardware, usb security dongles solution! We provide Software piracy protection tokens for end-to-end software copy protection services, advanced Sentinel HASP hardware products, and secure licensing solutions to safeguard your software and intellectual property.